Hipaa Security Risk Assessment Template Free
Hipaa security risk assessment template free - The establishment maintenance and continuous update of an Information Security Management System ISMS provide a strong indication that a company is using a systematic approach for the identification assessment and management of information security risks. HIPAA Certification for Employees Company and Products As per The Department of Health and Human Services DHHS which manages and is responsible for enforcing Health Insurance Portability and Accountability Act HIPAA Rule there is no company entrusted to certify an individual as HIPAA Certified or companies or products getting official HIPAA Certification. The Health Insurance Portability and Accountability or HIPAA violations happen when the acquisition access use or disclosure of Protected Health Information PHI is done in a way that results in a significant personal risk of the patient. Practice shall conduct an accurate and thorough risk analysis to serve as the basis for Practices HIPAA Security Rule compliance efforts. Practice shall re-assess the security risks to its ePHI and evaluate the effectiveness of its security measures and safeguards as necessary in light of changes to business practices and technological. The complete package has Risk Assessment guidelines matrix templates forms worksheets policies procedures methodologies tools recovery plan information on free resources and standards. Gartner gives a more general definition. HIPAA FERPA NY State Cybersecurity Regulations are only some of the laws that require a risk assessment to be done by impacted companies in the healthcare education and financial sectors. A vital advantage for security professionals is the ability to come up with robust vulnerability assessment reports. Cybersecurity risk assessments help organizations understand control and mitigate all forms of cyber risk.
The data security policy template below provides a framework for assigning data access controls. The Disaster Recovery template suite can help in complying with requirements of HIPAA Sarbanes-Oxley SOX FISMA and ISO 27002. An impermissible use or disclosure of protected health information is presumed to be a breach unless the covered entity or business associate as applicable demonstrates that there is a low probability that the protected health information has been compromised based on. The Health Insurance Portability and Accountability Act HIPAA Security Rule requires that covered entities and its business associates conduct a risk assessment of their healthcare organization. Once you have developed your policy based on the template be sure to expand it to cover new assets and operations as they are added to your business.
Free 9 Hipaa Security Risk Analysis Templates In Pdf Ms Word
From the University of Liverpool. In this article we will explore how to create a strong vulnerability. A vital advantage for security professionals is the ability to come up with robust vulnerability assessment reports.
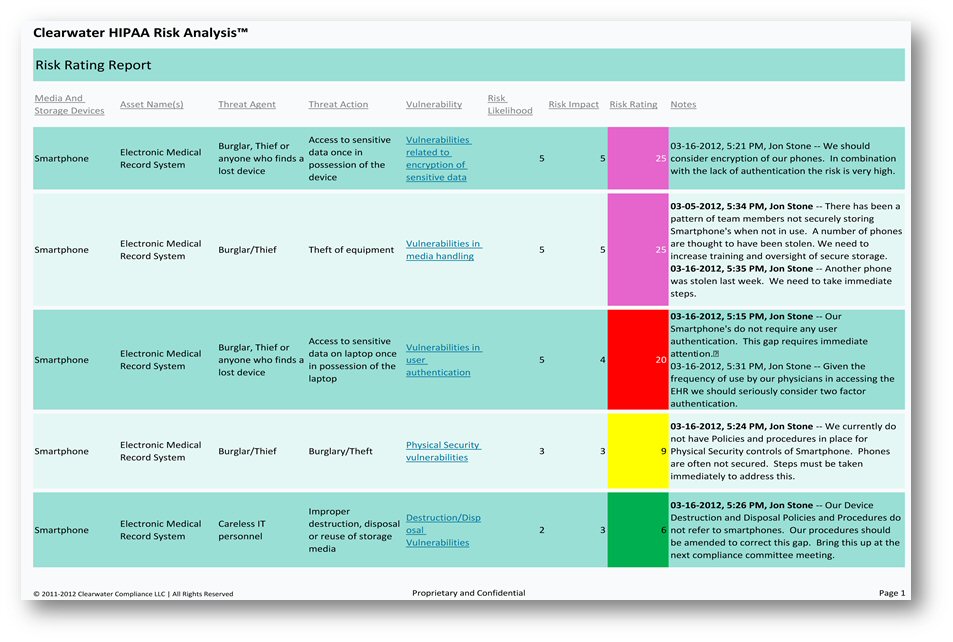
Show ImageHow To Start A Hipaa Risk Analysis Risk Analysis Security Assessment Analysis
The interview template allowed me to give them all of the information they needed in less than an hour. IT risk management can be considered a component of a wider enterprise risk management system. Risk assessments are nothing new and whether you like it or not if you work in information security you are in the risk management businessAs organizations rely more on information technology and.
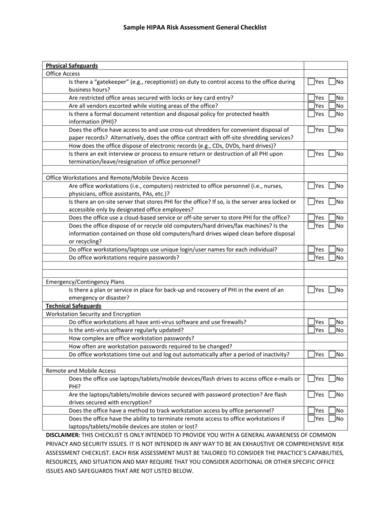
Show ImageAppendix 4 2 Sample Hipaa Security Risk Assessment For A Small Physician Practice Pdf Free Download
What is a HIPAA Violation. Cybersecurity risk assessments help organizations understand control and mitigate all forms of cyber risk. Or tap SAQs template library of surveys for regulations like HIPAA Basel 3 and SOX and industry standards like PCI.
Show ImageAppendix 4 2 Sample Hipaa Security Risk Assessment For A Small Physician Practice Pdf Free Download
The regulation concerns just about everyone that works with PHI. The complete package has Risk Assessment guidelines matrix templates forms worksheets policies procedures methodologies tools recovery plan information on free resources and standards. The establishment maintenance and continuous update of an Information Security Management System ISMS provide a strong indication that a company is using a systematic approach for the identification assessment and management of information security risks.
Show Image7 Hipaa Security Risk Analysis Examples Pdf Examples
HIPAA FERPA NY State Cybersecurity Regulations are only some of the laws that require a risk assessment to be done by impacted companies in the healthcare education and financial sectors. It can be. A vendor risk management questionnaire also known as a third-party risk assessment questionnaire or vendor risk assessment questionnaire is designed to help your organization identify potential weaknesses among your third-party vendors and partners that could result in a data breach data leak or other type of cyber attack.
Show ImageFree 7 Sample Security Risk Assessment Forms In Pdf Ms Word
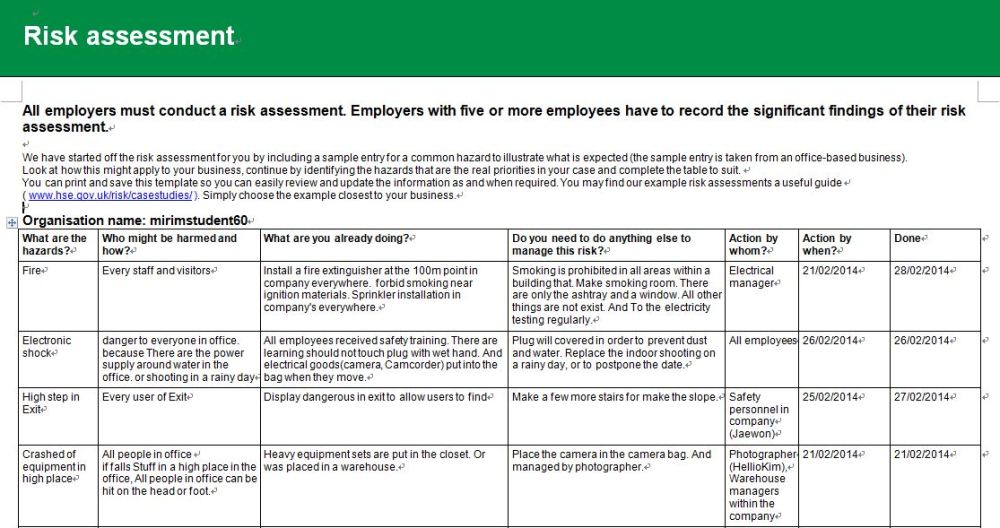
It can be. A vendor risk management questionnaire also known as a third-party risk assessment questionnaire or vendor risk assessment questionnaire is designed to help your organization identify potential weaknesses among your third-party vendors and partners that could result in a data breach data leak or other type of cyber attack. Decide who might be harmed.
Show ImageFree 9 Hipaa Security Risk Analysis Templates In Pdf Ms Word
A vendor risk management questionnaire also known as a third-party risk assessment questionnaire or vendor risk assessment questionnaire is designed to help your organization identify potential weaknesses among your third-party vendors and partners that could result in a data breach data leak or other type of cyber attack. Risk management for healthcare organizations helps to ensure the all businesses are compliant with HIPAA requirements and outlines potential risks that could occur in a healthcare organization such as clinical testing errors hospital facilities issues security breaches of protected health information PHI and more. What is a HIPAA Violation.
Show Image7 Hipaa Security Risk Analysis Examples Pdf Examples
Were working hard every day to ensure that cybersecurity risk receives adequate attention in our organizations. From the University of Liverpool. In this article we will explore how to create a strong vulnerability.
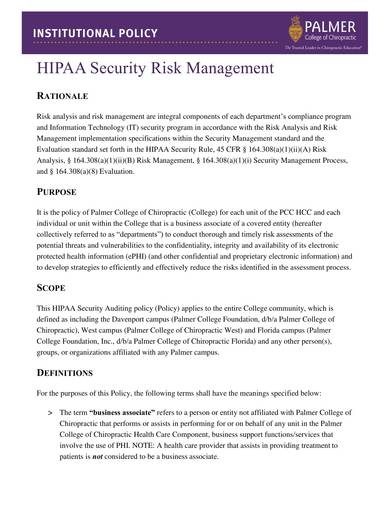
Show ImageHollandhart Com
This Disaster Recovery Plan DRP template suite can be used as a Disaster Planning Business Continuity Plan BCP by any organization. The regulation concerns just about everyone that works with PHI. Practice shall re-assess the security risks to its ePHI and evaluate the effectiveness of its security measures and safeguards as necessary in light of changes to business practices and technological.
Show ImageFree 9 Hipaa Security Risk Analysis Templates In Pdf Ms Word
The regulation concerns just about everyone that works with PHI. Risk management for healthcare organizations helps to ensure the all businesses are compliant with HIPAA requirements and outlines potential risks that could occur in a healthcare organization such as clinical testing errors hospital facilities issues security breaches of protected health information PHI and more. Once you have developed your policy based on the template be sure to expand it to cover new assets and operations as they are added to your business.
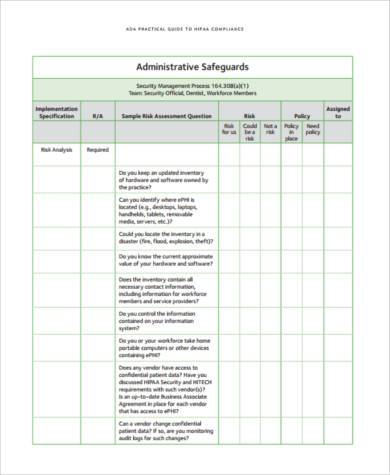
Show ImageThe data security policy template below provides a framework for assigning data access controls. HIPAA FERPA NY State Cybersecurity Regulations are only some of the laws that require a risk assessment to be done by impacted companies in the healthcare education and financial sectors. He is a specialist on legal and regulatory affairs and has several years of experience writing about HIPAA. Risk management for healthcare organizations helps to ensure the all businesses are compliant with HIPAA requirements and outlines potential risks that could occur in a healthcare organization such as clinical testing errors hospital facilities issues security breaches of protected health information PHI and more. Risk assessments are nothing new and whether you like it or not if you work in information security you are in the risk management businessAs organizations rely more on information technology and. Create a risk assessment policy that codifies your risk assessment methodology and specifies how often the risk assessment process must be repeated. It is a critical component of risk management strategy and data protection efforts. HIPAA Certification for Employees Company and Products As per The Department of Health and Human Services DHHS which manages and is responsible for enforcing Health Insurance Portability and Accountability Act HIPAA Rule there is no company entrusted to certify an individual as HIPAA Certified or companies or products getting official HIPAA Certification. The establishment maintenance and continuous update of an Information Security Management System ISMS provide a strong indication that a company is using a systematic approach for the identification assessment and management of information security risks. This Disaster Recovery Plan DRP template suite can be used as a Disaster Planning Business Continuity Plan BCP by any organization.
It does not mean that you are compliant but that you have been taught the terms of the Health Insurance Portability and Accountability Act and also. The complete package has Risk Assessment guidelines matrix templates forms worksheets policies procedures methodologies tools recovery plan information on free resources and standards. The Health Insurance Portability and Accountability or HIPAA violations happen when the acquisition access use or disclosure of Protected Health Information PHI is done in a way that results in a significant personal risk of the patient. Practice shall re-assess the security risks to its ePHI and evaluate the effectiveness of its security measures and safeguards as necessary in light of changes to business practices and technological. Cybersecurity risk assessments help organizations understand control and mitigate all forms of cyber risk. Or tap SAQs template library of surveys for regulations like HIPAA Basel 3 and SOX and industry standards like PCI. Yet many management teams and boards still struggle to grasp the extent to which cyber risks can impact organizational objectives. A vendor risk management questionnaire also known as a third-party risk assessment questionnaire or vendor risk assessment questionnaire is designed to help your organization identify potential weaknesses among your third-party vendors and partners that could result in a data breach data leak or other type of cyber attack. In this article we will explore how to create a strong vulnerability. A vital advantage for security professionals is the ability to come up with robust vulnerability assessment reports.
Being HIPAA certified means that you have successfully undergone a course designed to train and teach you the information you need to enable your business or organization to become HIPAA compliant. What is a HIPAA Violation. As security compliance and risk management professionals we know that cyber-attacks are increasing in frequency severity and creativity. IT risk management can be considered a component of a wider enterprise risk management system. A risk assessment is often a mandatory baseline that compliance regulations ask for says Sanjay Deo President of 24by7 Security. Once you have developed your policy based on the template be sure to expand it to cover new assets and operations as they are added to your business. How to do a risk assessment. A clear and concise vulnerability assessment report aids an organizations network security team in fixing and alleviating vulnerabilities the risks they pose and the possible occurrence of cyberattacks. It can be. Gartner gives a more general definition.