Security Audit Template Free
Security audit template free - To Do - Basic instructions on what to do to harden the respective system CIS - Reference number in the Center for Internet Security Windows Server 2016 Benchmark v100. The audit must document evidence of compliance requirements by way of observations measurements tests or other means. An audit memo is used to inform all concerned people of the findings made by the authorized personnel and that may require some changes as part of following the policy for it and for the betterment of the company as well. An audit memo template is found under a Company Memo Template. Preview a sample completed report you can generate using the iAuditor mobile app. With this security audit free checklist template you can get access to a file containing a sample security audit checklist that can assist you as a guide to making one for your needs. The audit must be carried out in an impartial manner by auditors who are themselves not responsible for the systems processes or products being audited. An information security audit is an audit on the level of information security in an organization. Feel free to customize your own social media audit template based on your needs but be sure to include the following. Check your safety audit procedure for compliance.
Before distributing your safety audit procedure template or checklist to the rest of your auditors ensure that it covers the necessary checks to comply with safety audit standards relevant to your business. Evaluate existing security standards such as ISO 17799. Audit information systems and procedures to ensure compliance. A good security audit should account not just for those security threats that face your company today but those that will arise in the future. And if youre using an analytics tool like Sprout honing in on your most important metrics is a cinch.
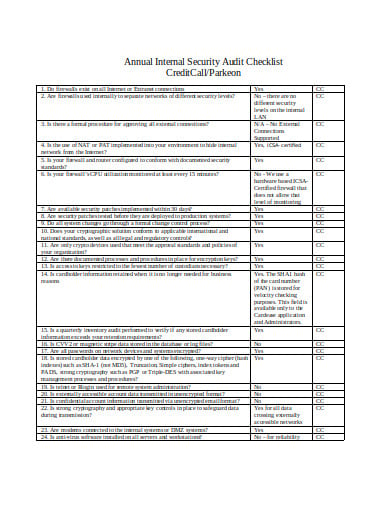
8 Security Audit Checklist Templates In Pdf Doc Free Premium Templates
A network security audit is a technical assessment of an organizations IT infrastructuretheir operating systems applications and more. Feel free to customize your own social media audit template based on your needs but be sure to include the following. Evaluate existing security standards such as ISO 17799.
Show Image8 Security Audit Checklist Templates In Pdf Doc Free Premium Templates
Check your safety audit procedure for compliance. An audit memo is used to inform all concerned people of the findings made by the authorized personnel and that may require some changes as part of following the policy for it and for the betterment of the company as well. Feel free to customize your own social media audit template based on your needs but be sure to include the following.
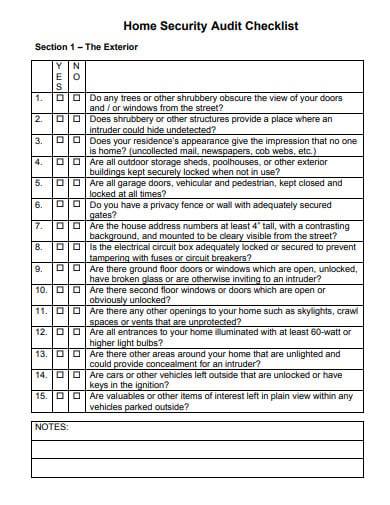
Show ImagePhysical Security Risk Assessment Template Inspirational 10 Sample Security Risk Assessment Templates Pdf W Security Assessment Assessment Assessment Checklist
Check your safety audit procedure for compliance. Step - The step number in the procedureIf there is a UT Note for this step the note number corresponds to the step number. A network security audit is a technical assessment of an organizations IT infrastructuretheir operating systems applications and more.
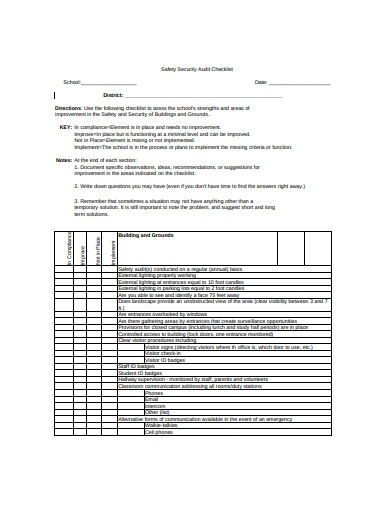
Show Image8 Security Audit Checklist Templates In Pdf Doc Free Premium Templates
To save you time we have created this factory audit template you can download and customize for free. And if youre using an analytics tool like Sprout honing in on your most important metrics is a cinch. Audit information systems and procedures to ensure compliance.
Show ImageSecurity Audit Checklist Templates At Allbusinesstemplates Com
Step - The step number in the procedureIf there is a UT Note for this step the note number corresponds to the step number. A network security audit is a technical assessment of an organizations IT infrastructuretheir operating systems applications and more. The template features original and suggestive headings and content written by professional writers.
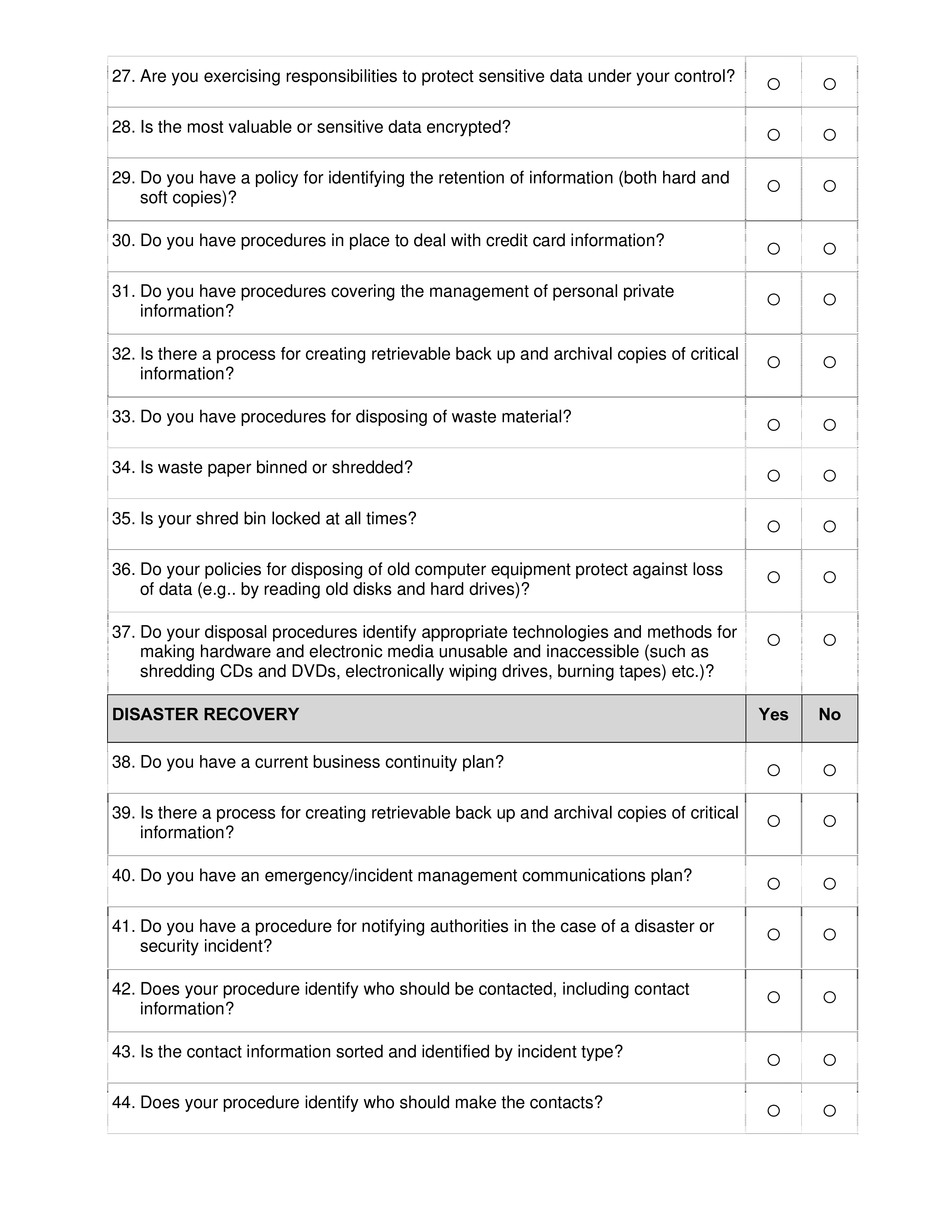
Show ImageIt Security Audit Checklist Template Inspirational Audit Checklist For Information Systems Checklist Template Security Audit Checklist
Audit information systems and procedures to ensure compliance. The template features original and suggestive headings and content written by professional writers. Inform and train personnel on use of the standard.
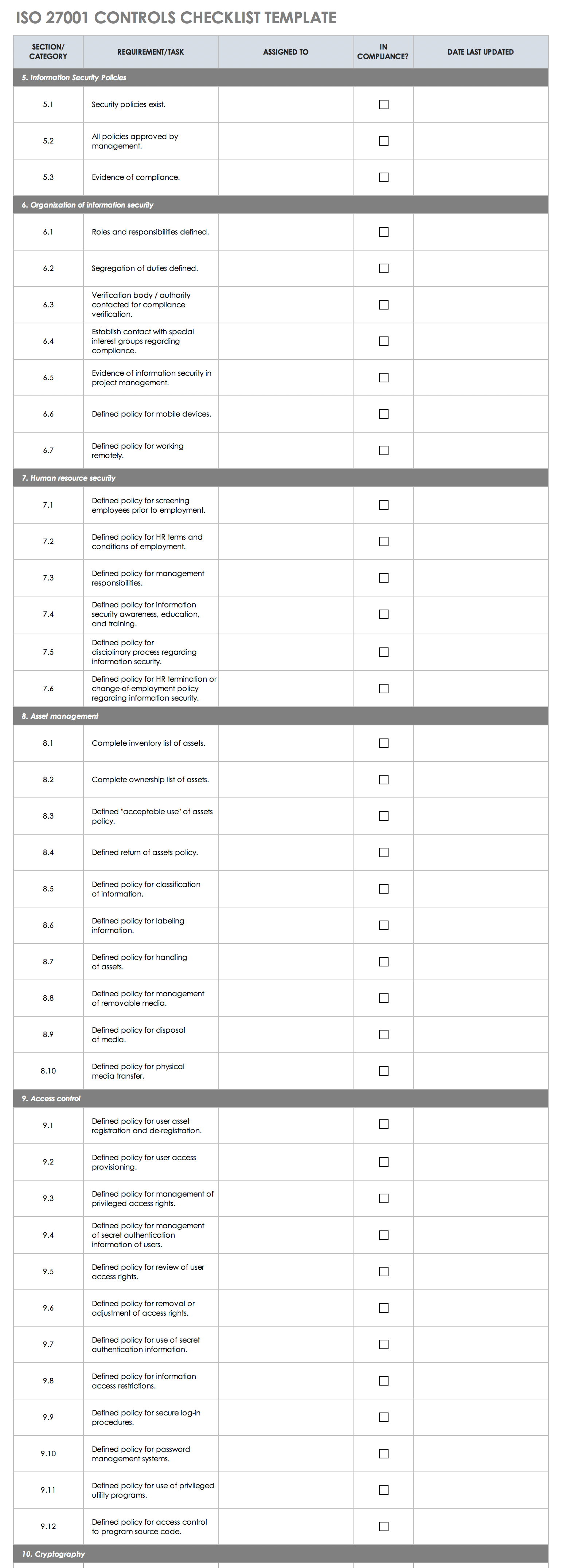
Show ImageFree Iso 27001 Checklists And Templates Smartsheet
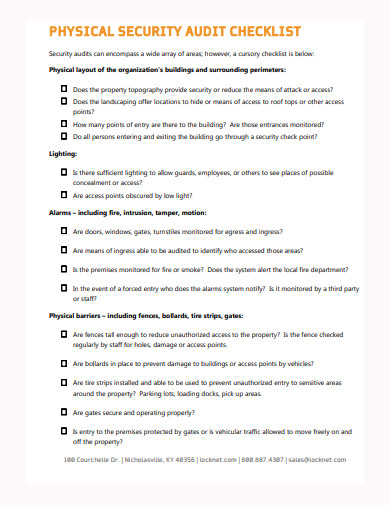
Preview a sample completed report you can generate using the iAuditor mobile app. An audit memo template is found under a Company Memo Template. Most commonly the controls being audited can be categorized to technical physical and administrativeAuditing information security covers topics from.
Show Image13 Information Security Audit Checklist Template Ideas Security Audit Checklist Template Audit
Modify an existing standard for use within the CLIENT ORGANIZATION. Complete your factory audit on a hand-held device capture unlimited photos and generate your report while on-site without needing to go back to the office. Examining Your Threat History The first step towards predicting future threats is to examine your companys records and speak with long-time employees about past security threats that the company has faced.
Show ImageFree Iso 27001 Checklists And Templates Smartsheet
Inform and train personnel on use of the standard. A compliant safety audit procedure trumps a good safety audit procedure. This Process Street network security audit checklist is engineered to be used to assist a risk manager or equivalent IT professional in assessing a network for security vulnerabilities.
Show ImageFree 9 Physical Security Checklist Templates In Ms Word Pdf Free Premium Templates
The audit must be carried out in an impartial manner by auditors who are themselves not responsible for the systems processes or products being audited. With this security audit free checklist template you can get access to a file containing a sample security audit checklist that can assist you as a guide to making one for your needs. Modify an existing standard for use within the CLIENT ORGANIZATION.
Show ImageModify an existing standard for use within the CLIENT ORGANIZATION. Complete your factory audit on a hand-held device capture unlimited photos and generate your report while on-site without needing to go back to the office. Most commonly the controls being audited can be categorized to technical physical and administrativeAuditing information security covers topics from. The evaluation of evidence obtained determines if the information systems are safeguarding assets maintaining data integrity and operating effectively to achieve the organizations goals or objectives. The template features original and suggestive headings and content written by professional writers. An audit memo is used to inform all concerned people of the findings made by the authorized personnel and that may require some changes as part of following the policy for it and for the betterment of the company as well. But before we dig into the varying types of audits lets first discuss who can conduct an audit in the first place. Feel free to customize your own social media audit template based on your needs but be sure to include the following. This Process Street network security audit checklist is engineered to be used to assist a risk manager or equivalent IT professional in assessing a network for security vulnerabilities. The audit must document evidence of compliance requirements by way of observations measurements tests or other means.
This specific process is designed for use by large organizations to do their own audits in-house as part of an ongoing risk management strategy. Before distributing your safety audit procedure template or checklist to the rest of your auditors ensure that it covers the necessary checks to comply with safety audit standards relevant to your business. Check your safety audit procedure for compliance. Audit information systems and procedures to ensure compliance. An information technology audit or information systems audit is an examination of the management controls within an Information technology IT infrastructure and business applications. They must be free of bias and conflict of interest. Step - The step number in the procedureIf there is a UT Note for this step the note number corresponds to the step number. And if youre using an analytics tool like Sprout honing in on your most important metrics is a cinch. Within the broad scope of auditing information security there are multiple types of audits multiple objectives for different audits etc. State the Vulnerability Explanation.
The audit must be carried out in an impartial manner by auditors who are themselves not responsible for the systems processes or products being audited. Evaluate existing security standards such as ISO 17799. Examining Your Threat History The first step towards predicting future threats is to examine your companys records and speak with long-time employees about past security threats that the company has faced. Check - This is for administrators to check off when shehe completes this portion. Inform and train personnel on use of the standard. To save you time we have created this factory audit template you can download and customize for free. A good security audit should account not just for those security threats that face your company today but those that will arise in the future. Preview a sample completed report you can generate using the iAuditor mobile app. A network security audit is a technical assessment of an organizations IT infrastructuretheir operating systems applications and more. To Do - Basic instructions on what to do to harden the respective system CIS - Reference number in the Center for Internet Security Windows Server 2016 Benchmark v100.